
Will your policy really pay out?
If you had a serious ransomware or payment‑fraud incident tomorrow, how confident are you that your cyber insurance would pay out in full and on time? Many mid‑market businesses only discover the answer to this very basic question is “no” when their insurer digs up the proposal form and compares it to what is actually happening on their network, in their backups and inside their finance processes.
The UK Government’s Cyber Security Breaches Survey 2025 shows that 43% of businesses reported a breach or attack in the last 12 months. Admittedly, this is down from 50% in 2024 (following an increased awareness of how cybercriminals can destroy great businesses) but medium and large organisations remain more at risk than small firms.
Within that statistic, the share of businesses reporting ransomware roughly doubled year‑on‑year, from under half a percent to around 1% – a material rise even if from a low base. Separate government research estimates the wider annual cost of cyberattacks to the UK economy at about £14.7 billion, roughly 0.5% of GDP, once disruption, recovery and lost business are included.
In the US, the FBI’s 2024 IC3 report records about 16.6 billion dollars in reported cybercrime losses in a single year, with cyber‑enabled fraud such as business email compromise responsible for a large share of that amount. The real issue for your business is not whether attacks happen. It is whether your controls, evidence and declarations hold up when the insurer starts asking hard questions.
Five critical controls insurers now expect to see
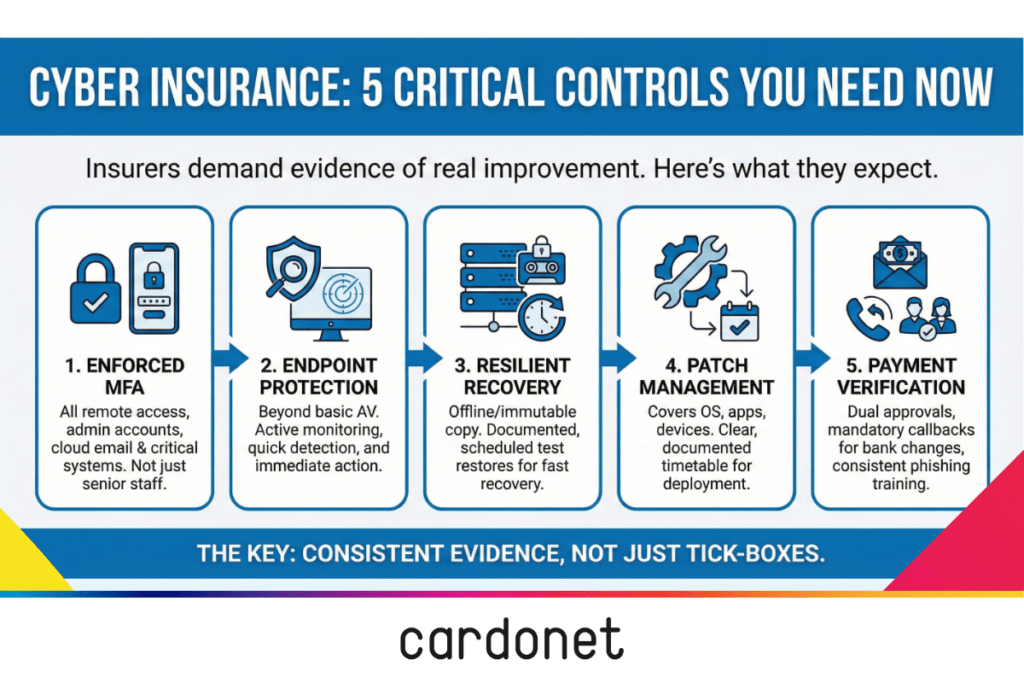
Insurers have moved past simple tick‑box questions and now expect to see real, year‑on‑year improvement in your cyber controls, backed by evidence they can inspect. In both the UK and US, the same weak spots keep coming up in underwriting calls, renewal questionnaires and post‑incident reviews.
1. Effective identity and access management
Underwriters expect strong, enforced multi‑factor authentication (MFA) for remote access, admin accounts, cloud email and key business systems, not just for a handful of senior users. In practice, that means conditional access rules, least‑privilege permissions and clear ownership for who approves, reviews and revokes access.
A managed IT partner should be able to show live MFA coverage, highlight legacy VPNs or third‑party tools that fall outside those controls and provide a simple plan for closing the gaps. If your answers look good but your logs tell a different story, a claim is likely to be challenged.
Why insurers care: if an attacker walks straight in on a weak password, they will ask why you ever said MFA was “in place”.
2. Endpoint protection and monitoring, not just antivirus
Basic antivirus on some laptops does not satisfy most cyber insurers. They want to know how you monitor endpoints across your estate, how quickly you detect suspicious behaviour, and what you do in the first minutes after you spot a problem.
In a well‑run environment, every laptop, desktop and server sits under centrally managed endpoint protection with logging and alerting into a service desk or security function. When an alert fires at night, there is a clear playbook for isolating the device, collecting evidence and starting recovery, so the incident can be documented and, if needed, reported to the insurer and regulators.
Why insurers care: slow or patchy detection turns a small incident into a big, expensive one.
3. Backups, recovery and continuity that survive ransomware
For insurers, the real test is not whether you have backups but whether you can recover quickly when everything looks encrypted or offline. The UK survey confirms that ransomware remains a persistent threat, even though it still affects a relatively small proportion of businesses overall.
That means multiple backup layers, including at least one offline or immutable copy, clear recovery time objectives for critical systems and documented test restores on a regular schedule. Your managed IT provider should be able to show when you last tested recovery for your finance system, how long it took and what you changed afterwards to make the next recovery smoother.
Why insurers care: strong, tested recovery is what stops a ransom demand turning into weeks of downtime and a huge claim.
4. Patch and vulnerability management with real follow‑through
Insurers do not take your word for patching anymore. External scans give them a direct view of unpatched internet‑facing systems, and if those scans do not match your answers about “regular patching”, confidence drops fast.
A mature patch process covers operating systems, key applications, network devices and cloud services, with a clear timetable for testing, deploying and documenting exceptions. Your IT partner should be able to produce straightforward reports showing outstanding critical vulnerabilities, how long they have been open and when they are due to be fixed, instead of vague statements about “keeping things up to date”.
Why insurers care: known, unpatched holes look like negligence, not bad luck.
5. Email, finance and payment verification that stops fraud
In both the UK and US, insurers are seeing more business email compromise and payment‑redirection fraud, often powered by AI‑generated messages that look and feel authentic. The IC3 report shows that business email compromise alone has driven multi‑billion‑dollar losses over recent years, making it one of the most expensive cyber‑enabled fraud types.
Underwriters now probe your payment‑approval processes, vendor‑bank‑detail changes and how you verify unusual instructions. Robust controls include dual approvals for sensitive payments, mandatory call‑backs to trusted numbers for bank‑detail changes and strict rules for creating new beneficiaries, backed by regular awareness training and realistic phishing simulations. The key is consistency under pressure: controls that colleagues bypass during busy periods will not impress an insurer after a loss.
Why insurers care: most of the really painful cheques they write now involve money leaving through email and payment fraud.
6. Incident response readiness that has been tested
Insurers increasingly ask whether you have an incident response (IR) plan, who leads it and when you last tested it. They also want to know how quickly you can identify, contain and report incidents, both to them and to regulators.
A good IR setup defines roles, escalation paths, decision‑making criteria and draft messages for customers and colleagues. In the UK, that sits alongside ICO expectations when personal data is involved, with the regulator’s own statistics showing regular data‑security incident reporting across sectors. In the US, differing state breach‑notification laws and sector rules add their own timelines, so you need a process your IT and legal advisers can follow even on a bad day.[9]
Why insurers care: a rehearsed response means fewer surprises, fewer mistakes and usually a smaller, cleaner claim.
How cyber insurers are changing the rules every year
Cyber insurance used to be a short form and a quick chat about limits and price. That world has gone. In both the UK and US, insurers now price you on how risky you look in practice, not on how tidy your proposal form seems.
In the UK, official surveys confirm that a substantial minority of organisations are still experiencing attacks, and government analysis highlights the wider economic cost of those incidents across sectors. In the US, the FBI’s IC3 report records 16.6 billion dollars in reported losses for 2024, with cyber‑enabled fraud such as business email compromise taking the largest share by value and other attack types like ransomware battering critical infrastructure and operations.
That has turned renewals into something closer to a mini audit:
- Longer, more technical questionnaires on MFA, backups, segmentation and endpoint monitoring.
- External perimeter scans to cross‑check your answers with what is visible from the internet.
- Requests for policy documents, process descriptions and selected logs or incident summaries where there have been claims.
Most mid‑market firms have some gaps when they first go through this. The ones that progress fastest are clear about those gaps and treat each renewal as a step‑change in maturity rather than a box‑ticking exercise.
Premiums, deductibles and sub‑limits: what weak controls cost you
Insurers do not care what you hope will happen. They care what your day‑to‑day operations look like when something goes wrong. As claims have grown, they have become far more aggressive in using premiums, deductibles and sub‑limits to separate stronger‑control firms from weaker ones.
Broadly, you will see the impact in three areas:
- Premiums: Firms with strong, evidenced controls can often negotiate flatter or slower‑rising premiums. Firms with patchy controls get moved into more expensive buckets quickly.
- Deductibles: Ransomware, business interruption and fraud deductibles tend to be higher when insurers doubt your ability to prevent or contain incidents.
- Sub‑limits and exclusions: Social engineering, data restoration, incident response and regulatory‑cost cover are often capped or tightly conditioned for firms that cannot demonstrate robust controls.
Insurers put weaker‑control firms in costlier brackets. If you can prove your controls actually work, you usually avoid that bracket.
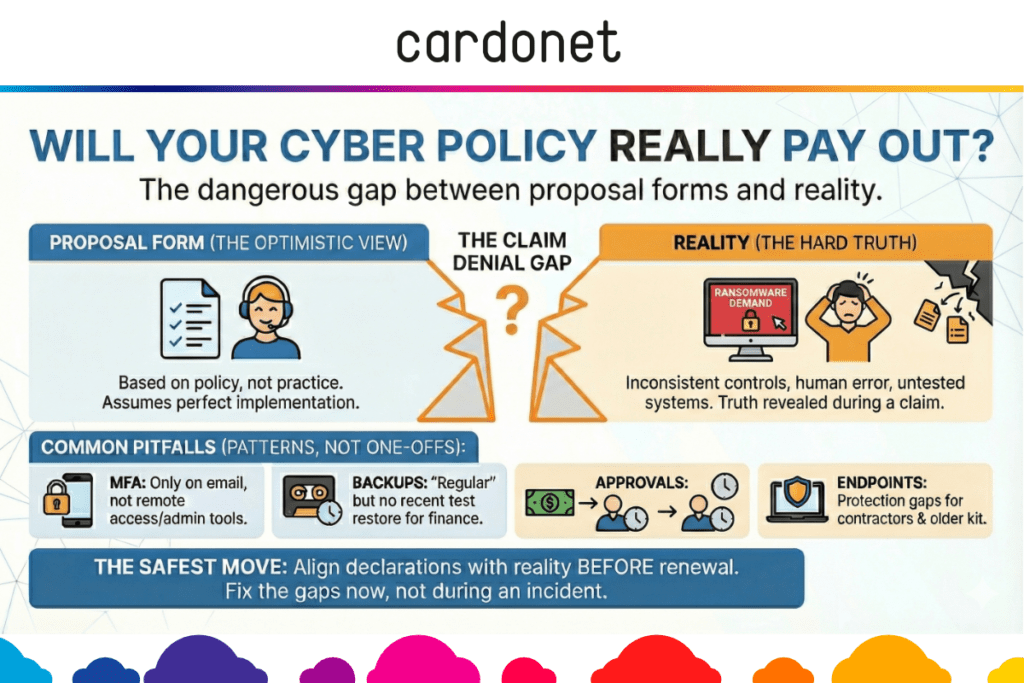
The dangerous gap between what you declare and what actually happens
The most dangerous weakness is often not the attacker. It is the gap between what you declare on the proposal form and what actually happens in your systems and processes.
Typical examples include:
- MFA declared as “in place” but only used for Microsoft 365 and a few admin tools, with remote access and third‑party connections left on passwords alone.
- “Regular backups” claimed, but no recent recovery test for your finance system and backups stored online where ransomware can reach them.
- “Endpoint protection across all devices” while contractors, personal laptops and legacy servers fall outside central management.
- “Dual approval for payments” in policy documents, but one‑person approvals in practice when signatories are travelling or under time pressure.
The ICO’s trend data shows that many incidents still come down to basic process failures and human error, not sophisticated, targeted exploits. When an insurer investigates a claim, they look closely at whether controls were implemented as described, whether exceptions were documented and whether incident and recovery timelines align with your declarations. If there is a material mismatch, they have room to delay, reduce or in serious cases decline payment.
Most mid‑market firms have at least some of these gaps. The crucial question is whether you find and fix them before an incident, or whether an insurer finds them afterwards during a claim.
Why leadership, finance and IT need to act as one team
Cyber insurance now cuts across risk management, finance and technology. If any one of those is missing from the conversation, you are likely to leave money or coverage on the table.
- Leadership sets risk appetite and decides how much disruption, data loss and downtime the business is prepared to tolerate
- Finance focuses on premiums, deductibles, likely uninsured losses and whether cover still matches the balance sheet
- IT and your managed providers own the real‑world controls, from MFA and backups to incident response and payment processes
The mid‑market businesses that handle rising insurer expectations best usually share ownership of questionnaires between finance and IT, with leadership close enough to understand trade‑offs, while regular IT and cyber audits feed into renewal planning, not just technical backlogs.
They also maintain a short, practical evidence pack that includes MFA coverage summaries, backup and recovery‑test logs, patch‑status reports and brief incident write‑ups.
This turns insurer conversations into informed risk discussions instead of last‑minute scrambles.
Turning renewals into a strategic review, not a form‑filling exercise
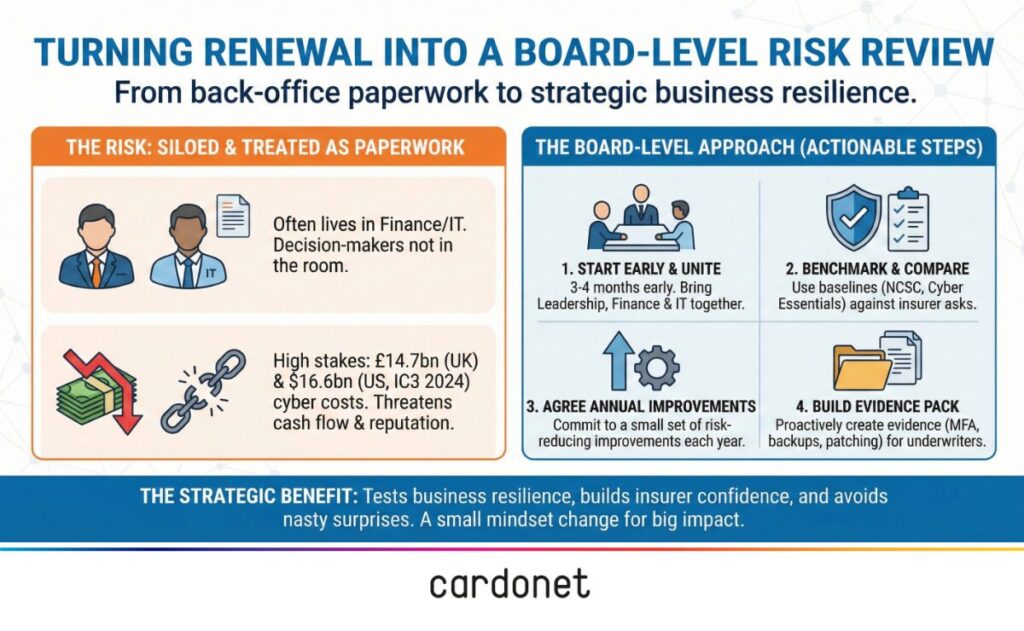
A cyber insurance renewal is one of the few times each year when your business is forced to look at cyber risk as a whole. If you treat it as a form‑filling exercise, you waste a golden opportunity.
In the UK, government and NCSC guidance encourage organisations to adopt practical baselines like Cyber Essentials and to think in terms of resilience and recovery as well as prevention. In the US, official reports on cybercrime losses and cyber insurance trends have pushed many boards to bake cyber risk into normal financial decisions instead of treating it as a side topic.
The more resilient mid‑market firms now:
- Plan a joint finance‑IT‑leadership session three to four months before renewal
- Review current controls against insurer questionnaires and recognised best‑practice guidance such as the NCSC small business guide
- Pick a small number of improvements that will both reduce risk and strengthen their position when negotiating premiums and terms
If you already work with a managed IT partner, this is the conversation where you should ask for clear, detailed input on where you are exposed, not just a clean bill of health.
If you do not, renewal season is a strong sign that it is time to bring in a partner who can connect technology, operations and insurance expectations.
What continuous managed IT and security actually look like in practice
You do not buy resilience once. You earn it in the small, routine tasks your IT team carries out every week.
In a typical mid‑market business, a mature managed service relationship will include:
- 24/7 monitoring of key systems and endpoints, with clear triggers for when engineers are alerted and how they respond
- Structured patch cycles, with planned maintenance windows, short exception lists and visible deadlines
- Backup routines that include offline or immutable copies for critical systems, plus scheduled test restores that prove you can hit your recovery targets
- Simple, clear incident runbooks so that when something breaks, everyone knows who leads, who talks to the insurer and who keeps customers informed
Every one of these activities leaves an evidence trail in tickets, reports and logs. That trail is exactly what insurers and regulators want to see after an incident, because it shows you took reasonable steps before the attack, not just after it.
Why this matters for business leaders
For a managing director or finance director, cyber insurance is now a core tool for protecting cash flow and balance sheet strength when something goes badly wrong. It is not just another line in the insurance schedule.
In the UK, official surveys underline how common cyber incidents remain and how much disruption and cost they can cause across sectors, even as overall breach rates move slightly down. In the US, government and law‑enforcement data shows rising reported cybercrime losses with business email compromise and other fraud‑type scams dominating by value, and ransomware and similar attacks often driving the most visible operational disruption.
Treating cyber insurance as a strategic review, supported by strong IT operations and realistic security controls, protects more than your premiums. It helps you keep serving customers when others are scrambling. It also shows boards, investors and regulators that cyber risk is being managed with the same discipline as any other major financial exposure.
If you are a CEO or founder, the decisions this points you towards are simple:
- Treat cyber insurance renewal as a board‑level risk review, not paperwork
- Fund a basic but serious control uplift around MFA, backups and payment checks, and make sure you can evidence it
- Make sure finance and IT sign off the same story before you sign the proposal form
Protecting your business: next steps
If you want your policy to respond properly when you need it, your IT reality, your documentation, and your insurer declarations must line up.
That does not require a massive transformation programme, but it does require a clear plan and a partner who understands both technology and insurer expectations.
Over the next 30–90 days, you should:
- Run a focused cyber security audit that maps your controls against what insurers now ask for, including MFA, endpoint protection, backups, patching, incident response and payment processes
- Build a short evidence pack for renewals, with named owners for MFA, backups, patching, monitoring and finance processes so nothing depends on one person’s memory
- Set up a quarterly review with your managed IT partner to track improvements against insurer questions and record what has changed since last year
Typical investment in tightening MFA, backups and payment controls sits at a fraction of the potential losses from a serious incident, especially once downtime, lost deals and uninsured loss are considered.
While exact figures vary by business, it is common for direct and indirect costs from a major cyber event to run well beyond the initial claim value.
Cardonet helps organisations carry out practical cybersecurity audits that feed directly into cyber insurance readiness and renewal discussions, not just technical reports.
If you want to understand where your declarations and day‑to‑day IT operations are out of sync, arrange a conversation with Cardonet.
Together we can review current controls, identify where insurers are most likely to challenge and agree a realistic plan to close the gaps before they become a problem for your business.
Cyber insurance and IT controls: FAQs
1. What cyber controls do UK and US insurers now expect as standard for mid‑sized businesses?
Most underwriters now expect enforced MFA on key systems, centrally managed endpoint protection, resilient and tested backups, structured patching and clear incident response and payment‑verification processes. These expectations align closely with UK government and NCSC guidance, as well as the kinds of controls highlighted in official US cybercrime and cyber insurance reports.
2. How do AI‑driven attacks and fraud affect cyber insurance premiums and cover?
AI is making phishing and fraud more convincing, contributing to higher reported losses and a greater share of claims linked to business email compromise and other cyber‑enabled scams. Insurers put weaker‑control firms into higher‑priced buckets and tighten sub‑limits and deductibles for fraud and ransomware. If you can show that your controls actually work in practice, you usually avoid the worst of that.
3. Can a cyber insurer refuse to pay if my IT setup is different from what I put on the proposal form?
If there is a significant gap between what you declared and what was actually in place, insurers may delay, reduce or, in serious cases, decline a claim under misrepresentation or non‑disclosure clauses. Regulators’ data shows that many incidents come down to missing or poorly implemented controls, so insurers have a strong incentive to examine whether your declarations match real‑world practice.
4. How often should my business review IT security controls in line with our cyber insurance policy?
At a minimum, you should complete a structured review before each renewal, but many organisations now run quarterly reviews that link technical change to insurance expectations and regulator guidance. Using frameworks such as the NCSC small business guide and Cyber Essentials helps you base those reviews on recognised best practice rather than one‑off checklists.
5. How can a managed IT partner help me negotiate better cyber insurance terms in the UK and US?
A managed IT partner can translate insurer questions into specific controls, provide clear evidence of MFA coverage, backups, patching and monitoring, and support rapid investigation when something goes wrong. This gives brokers and underwriters more confidence in your risk profile and helps secure more favourable pricing and fewer restrictive conditions.

You must be logged in to post a comment.